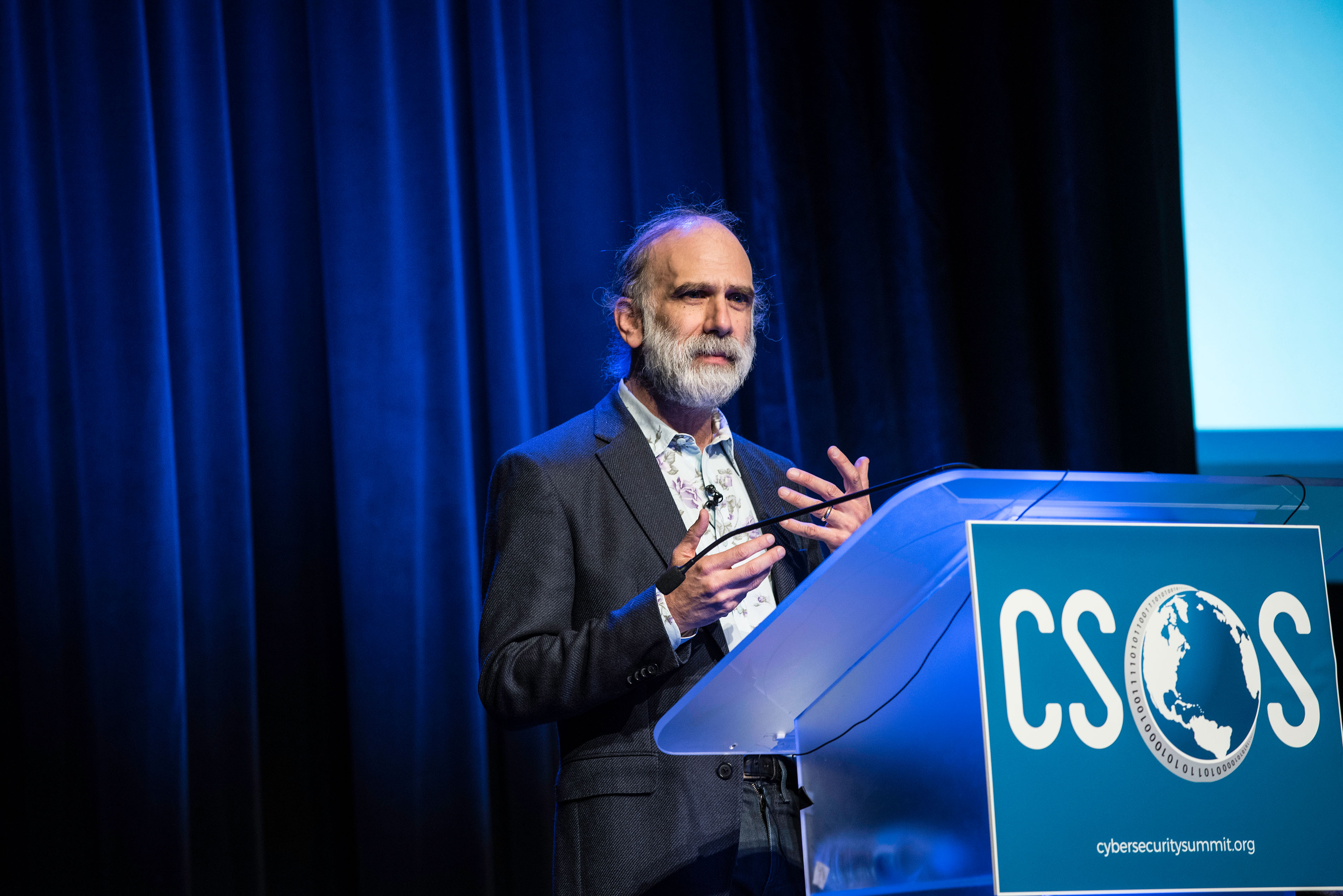
“Everything today is a computer,” declared Cyber Security Summit 2018 keynoter Bruce Schneier, CTO, IBM Resilient. IoT is the “computerization” of the whole world, making exponentially complex the safeguarding of most of our devices.
“Everything today is a computer,” declared Cyber Security Summit 2018 keynoter Bruce Schneier, CTO, IBM Resilient. IoT is the “computerization” of the whole world, making exponentially complex the safeguarding of most of our devices.
Schneier, author of many security-related books and the popular Schneier on Security blog, presented “Click Here to Kill Everybody,” the name of both his presentation and his latest book. He listed six lessons to take from the dynamics influencing cybersecurity today.
- Most software is poorly written and insecure because it’s designed to be fast and cheap, instead of good.
- The Internet was never designed with security in mind.
- Device functionality can be extended to perform more than one routine. For instance, people can add apps to your cell phone via a computer. Your digitally connected refrigerator can send spam.
- Complexity produces larger attack surfaces as more devices connect to the Internet and to each other. Attacks will always be easier than defense.
- The new combinations of connections introduce a huge number of new vulnerabilities. Examples: Target Corp.’s hacking via an HVAC provider; a casino that lost a high-roller contact list via an insecure connection to a fish tank.
- Attacks always get easier, better (from the attacker’s viewpoint) and faster as algorithms produce better techniques.
Risks are changing, Schneier said. Vulnerabilities are heightened by privacy violations. The CIA lists three elements of concern: confidentiality, integrity and availability. While confidentiality is still important, Integrity and availability introduce risks to life and property, he said.
Peril has taken a large step forward because now a victim’s safety is at risk. For instance, a hacker could access someone’s personal health information and change the record of their blood type. A hacked chip could prevent a car from braking or stop a pacemaker from functioning. In a worst-case scenario, someone with treacherous intent might try to cause a “class break” in which all like devices of a type would stop working.
Other factors enter into security and Schneier listed a litany of risk factors. Patching brings fixes for new vulnerabilities – but low-cost devices have nowhere to add a patch. DVRs are an example of a device for which there is no fix, and replacement of the old device is the fix. “We have no idea how to secure 40-year-old software,” Schneier said.
Authentication is another challenge and it’s going to be tested more than ever. Passwords are weak and secret questions are not secure. Thing-to-thing authentication is coming as our devices talk to each other.
“We don’t know how to do that (kind of security),” Schneier said.
The supply chain introduces another risk, Schneier said, mentioning the Russian-made Kaspersky security software that some worry spies on users as an example. In 2008, ISIS created encryption software. Components are manufactured all over the world by people of all stripes and end up in devices with little vetting beyond functionality.
There are fake apps in Google Play Store, Schneier said. One can hack an iPhone using a malicious replacement screen. He noted that the technology industry is deeply international in a way we can’t untangle, and that is a vulnerability.
“The fix is policy. Law and tech have to work together. Law can subvert tech, and Snowden showed that tech can subvert law,” he noted.
The choice is between smart government involvement and stupid government involvement, he said.
“There is no alternative to improving safety without the influence of government,” he said.
Schneier asked his audience, “Did anybody watch the Facebook hearings (before Congress)? This is what we get when people don’t understand technology … we can’t get good policy.”
“Don’t think you’ll get anything done without government regulation. Self-regulation is a stalling tactic,” he said.
[ Photo Credit: Bruce Silcox Photography ]