“If you’re in cyber security, you’ve got a problem,” said Scott Borg, CEO of Cyber Consequences Unit. C-level cyber security people may be topped out career-wise in their organizations because management may not understand what they do and security terminology is alien to businesspeople.
Speaking on the “Economics of Cybersecurity,” Borg advocated that his security audience explain the value they produce in economic terms that are familiar to other C-level executives. Otherwise, cybersecurity executives may be left out of the C-level loop because their terminology in describing their work defending company assets is unfamiliar to people who work in other business areas.
The work you do is critical to your organization because attackers want to steal your business information. If you’re a cyber executive and your work and contributions aren’t well understood, when your company gets hacked, you may be out of a job, Borg said.
“Economics can help you convincingly explain why you’ve done the right thing to save your job,” he noted.
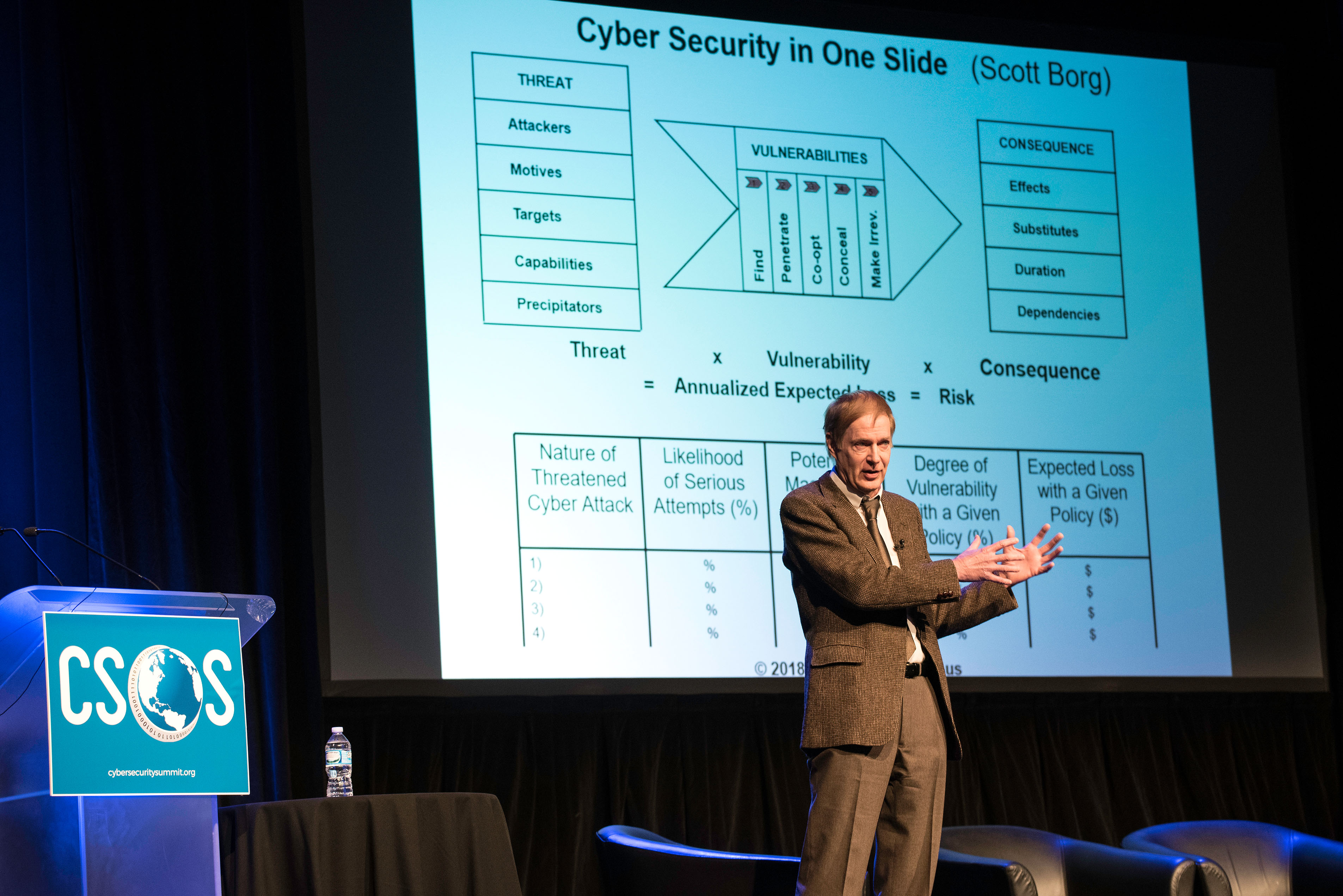
Risk is measured in degrees of expected loss per year, Borg said, referring to the US Cyber Consequences Unit risk model. In part, the model uses an equation showing threat multiplied by vulnerability multiplied by consequences to produce an estimated numerical risk value of expected loss per year. Borg said various scenarios can be compared using this model.
The model also solicits qualitative inputs including suspected attackers, motives, targets, capabilities and attack triggers to help practitioners identify who may be attacking them, and why. Best case scenario, elements considered in the model may be modified to deny the attacker’s goal and make the attack infeasible. Attackers apply the same criteria as businesses, Borg said. If something is too expensive, too risky or offers too little chance of success, attackers likely will seek other opportunities.
By comparing various combinations of inputs, a security officer can show others how they changed the company’s exposure, reduced risk and added value. In familiar terms, security executives can explain how they reduced expected loss in ways that others can understand. They also can quantify the elements that drive profitability.
“Don’t trust absolute numbers, if you see them. Precise numbers are fraudulent,” he cautioned. “Analysis may only give an order of magnitude answer – almost always good enough – (for example) hundreds of thousands, not millions.”
A full understanding of the attackers is the goal of the model. “Look at who is attacking you in terms of psychographics,” he suggested. “What are the attacker’s motives for the attack?”
A lengthy checklist of questions yields answers that stimulate insights to drive the model and derive good decisions. What are the attackers’ capabilities? Who are their targets? What do they hope to gain through their attack? What are their resources and capabilities? How large a population supports them? What thresholds will trigger an attack?
Borg stressed the importance of recognizing your organization’s value propositions and factors that produce value since those are likely what an attacker wants to co-opt or steal. “How does your organization create value,” he questioned. “What makes your organization indispensible?”
“Consequence is value created before an attack minus value created after an attack,” he said.
Attackers can interrupt, corrupt and undermine company files. Five things attackers must do to be effective, Borg said, are:
- Find the target
- Penetrate the perimeter
- Co-opt the process
- Conceal their presence
- Change something significantly
He suggested that penetration mentality and trying to keep attackers out of the system persists in cybersecurity. However, we’re now getting better at making it hard for attackers to find what they’re looking for.
Security practitioners need to identify the “hard spot” – the part that can most easily be altered to thwart the attack.
“Your goal is not to stop the attacker,” he said. “Your goal is to increase attacker cost.”
You can estimate what actions to take to reduce risk and vulnerability and “The benefit to the company is large and fairly immediate.”
Helping peers gain a thorough understanding of cybersecurity and risk can earn that CISO a place at the table in C-suite strategy meetings, Borg said.
“There are right answers,” he said. “You can explain everything in terms the CFO can understand.”
[ Photo Credit: Bruce Silcox Photography ]